Industries
Resources
Industries
Resources
Proud of our extensive industry experience and comprehensive application scenarios, GeeTest has delivered professional cybersecurity services to leading enterprises worldwide.


360,000
+
670,000
+
12
Years

GeeTest offers an ML-powered security system to address various threats. Whether you’re starting from scratch, enhancing existing capabilities, or building a complete risk management system, GeeTest can meet your needs.

 Behavior Verification
Behavior Verification Device Fingerprinting
Device Fingerprinting Business Rule Engine
Business Rule Engine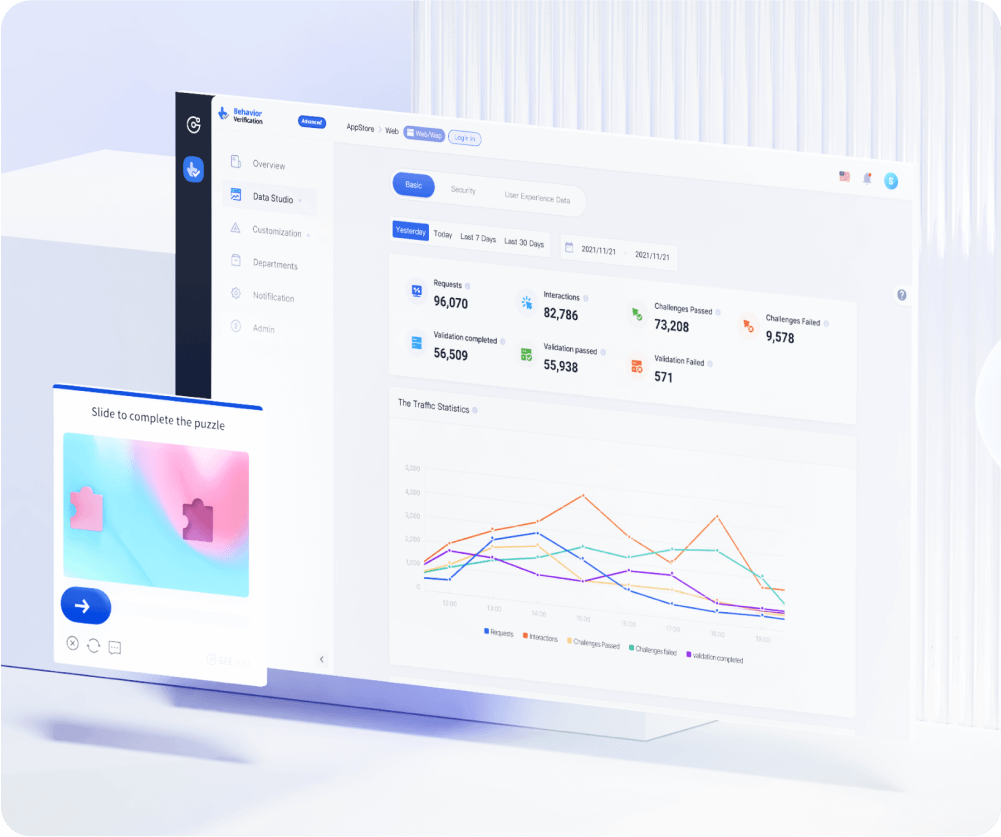
Smart defense against bot attacks
GeeTest's newest adaptive CAPTCHA combats sophisticated bots with dynamic security and offers a customizable design for a seamless experience for enterprises and end users.Behavior verification enhanced by 7-layer dynamic protection.
Optimizing conversion rate with ease-of-use design.
Easily integrated for WEB, WAP, iOS, Android, Html5.
Multilingual support and global deployment.
The increasing online fraud calls for a more secure and proven cybersecurity platform. GeeTest has been tested in thousands of scenarios and can adapt to various application environments.

Prevent unauthorized access and protect against financial losses

Protect your customers’ data. Prevent financial and brand reputation loss

Prevent scalpers from snatching tickets and making profits from reselling

Prevent valuable content and sensitive data from being stolen

Prevent fabricated and simulated numbers of clicks and views by real users

Prevent fraudulent transactions and payment scams to maintain customer trust
GeeTest's pursuit of experience resists cyber enemies invisibly.
GeeTest's pursuit of experience resists cyber enemies invisibly.
Join us with 360,000+ protected domains now!
安全业务专家将会尽快联系您

简单向我们描述业务背景和当前需求

根据您的诉求整理对应的方案,并达成一致

根据方案,我们一起部署落地,并观察效果
企业名称/站点名称:
请验证手机号: